WEP Cracking: Difference between revisions
From ivc wiki
Jump to navigationJump to search
No edit summary |
No edit summary |
||
| Line 5: | Line 5: | ||
* '''[http://www.isaac.cs.berkeley.edu/isaac/wep-faq.html (In)security of the WEP algorithm by Nikita Borisov, Ian Goldberg, and David Wagner]''' | * '''[http://www.isaac.cs.berkeley.edu/isaac/wep-faq.html (In)security of the WEP algorithm by Nikita Borisov, Ian Goldberg, and David Wagner]''' | ||
* [http://www.isaac.cs.berkeley.edu/isaac/mobicom.pdf Intercepting Mobile Communications:The Insecurity of 802.11 paper] | |||
[[Image:Wep_encryption.png|right]] | [[Image:Wep_encryption.png|right]] | ||
Revision as of 21:56, 26 August 2009
WEP is infamously known as the broken wireless security protocol. A design flaw was discovered in 2001 and after several cascading discoveries it's now possible to crack a WEP protected network within minutes. WPA is the successor to WEP and features a better but not perfect security protocol.
Background
There are now many sources that describe the vulnerability in detail and APR replay to generate traffic, but this is a short summary. For an throughout explaination on how WEP is implemented and the vulnerabilities, see the link below.
- (In)security of the WEP algorithm by Nikita Borisov, Ian Goldberg, and David Wagner
- Intercepting Mobile Communications:The Insecurity of 802.11 paper
Parts:
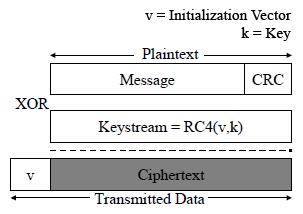
- WEP encryption:
- 24-bit unencrypted initialization vector + 104-bit key (13 characters/bytes), 128-bit key
- Used to generate RC4 cipher stream
- XOR the message
- Encrypted network packets
- ARP replay:
- On the basis that the first 12-bytes of ARP packets always stays the same
- Capture one ARP packet
- Inject back to into the network to stimulate traffic
- Capture 10-20 000 ARP (or other data) packets to build a Initialization Vector table (only 2^24 possibilities)
- Key attack:
- Find Initialization Vector collisions where two ARP ciphertexts are the same (2^24 possibilities)
- XOR back first 12-bytes using the known plain-text ARP data
- RC4 stream cipher is revealed for that specific IV
- Find enough collisions
- Use the collected data to build a table of IVs and RC4 stream ciphers and use it to gain a statistical factor for the remainder of the missing key bytes, 104-bit (13 character) key