Xbox 360 Kernel: Difference between revisions
No edit summary |
No edit summary |
||
| Line 47: | Line 47: | ||
=== CPU / Per-Box Key === | === CPU / Per-Box Key === | ||
The CPU Key is used to only encrypt the Keyvault. By altering the the Keyvault you can change the lockdown counter on a vulnerable kernel, re-encrypting the Keyvault with the CPU Key, and downgrading from a non-vulnerable by re-flashing the NAND. | The CPU Key is used to only encrypt the Keyvault. By altering the the Keyvault you can change the lockdown counter on a vulnerable kernel, re-encrypting the Keyvault with the CPU Key, and downgrading from a non-vulnerable by re-flashing the NAND. Still need a prior NAND dump from Infectus (dump32 Linux dumps miss the ECC bits). | ||
The CPU Key can be found by combining fusetset #03 + #05 (or #04 + #06). The final string should be 16 bytes long, e.g xxxxxxxxxxxxxxxxyyyyyyyyyyyyyyyy. | The CPU Key can be found by combining fusetset #03 + #05 (or #04 + #06). The final string should be 16 bytes long, e.g xxxxxxxxxxxxxxxxyyyyyyyyyyyyyyyy. | ||
| Line 54: | Line 54: | ||
==== XeLL Output ==== | ==== XeLL Output ==== | ||
This shows the XeLL output | This shows the XeLL output from the serial cable method. | ||
Xe>! | Xe>! | ||
XeLL - Xenon linux loader 0.1 | XeLL - Xenon linux loader 0.1 | ||
Revision as of 23:48, 11 August 2007
Boot-up
TheSpecialist, Xboxhacker.net:
Well from power-on: 1. 1BL (first bootloader, stored in ROM), this loads decrypts and starts: 2. CB (2BL, 2nd bootloader, stored in NAND), this this loads decrypts and starts: 3. CD. This loads, decrypts and decompresses CE, which contains the base kernel + base HV (Hypervisor). It also loads decrypts and then starts: 4. CF. This loads, decrypts and decompresses CG, which contains the patches for kernel and HV. It then applies the patches and starts up the patched HV and then the patched kernel. Then it boots dash. So basically it's like: 1BL -> 2BL -> patch kernel and HV and start them -> boot dashboard. Every step also checks signature for the next step of course.
View Content
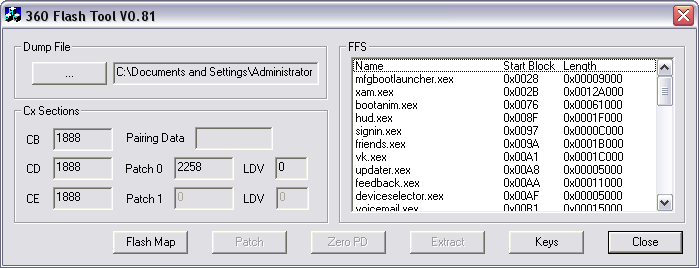
To view the content of the dumped NAND flash download the latest version of 360 Flash Dump Tool and open the BIN file.
To decode all of the encrypted content you need the CPU Key located in the fusesets (there are 12) and the 1BL located in the CPU ROM. These are found using the King Kong shader exploit and XeLL (Xeon Linux Loader) on vulnerable firmware version, e.g 4532 and 4548.
1BL Key
The 1BL is the 'First Boot Loader' and is stored in the ROM inside the CPU. The loader is 32KB and the 1BL key is the same for all Xbox 360 machines. To dump the 1BL you need to compile dump32.c and execute it to extract fuses.txt, nand.bin and 1bl.bin.
Due to the nature of the legality behind the static key, you have to find it yourself (think AACS). To find the key inside 1bl.bin you need to install IDA and disassemble using the PPC processor setting.
Discover the 1BL key [1]:
Start at sub_4240 and remember that encrypted data is at 0x8000_0200_C800_0000 and destination of unencrypted data is 0x8000_0200_0001_0000 and key is 0x10 bytes long. %rtoc is 0. Don't get sidetracked digging too deeply into each and every bl off sub_4240.
Fuses
There are 12 fusesets and they form the fundament for the Xbox 360 hypervisor security [2]. The fusesets (12) are located inside the CPU and thus hard to modify externally.
Fuseset #01 - 00: c0ffffffffffffff Fuseset #02 - 01: 0f0f0f0f0f0f0ff0 Fuseset #03 - 02: 0f00000000000000 Fuseset #04 - 03: xxxxxxxxxxxxxxxx Fuseset #05 - 04: xxxxxxxxxxxxxxxx Fuseset #06 - 05: yyyyyyyyyyyyyyyy Fuseset #07 - 06: yyyyyyyyyyyyyyyy Fuseset #08 - 07: 0000000000000000 Fuseset #09 - 08: 0000000000000000 Fuseset #10 - 09: 0000000000000000 Fuseset #11 - 0a: 0000000000000000 Fuseset #12 - 0b: 0000000000000000
CPU / Per-Box Key
The CPU Key is used to only encrypt the Keyvault. By altering the the Keyvault you can change the lockdown counter on a vulnerable kernel, re-encrypting the Keyvault with the CPU Key, and downgrading from a non-vulnerable by re-flashing the NAND. Still need a prior NAND dump from Infectus (dump32 Linux dumps miss the ECC bits).
The CPU Key can be found by combining fusetset #03 + #05 (or #04 + #06). The final string should be 16 bytes long, e.g xxxxxxxxxxxxxxxxyyyyyyyyyyyyyyyy.
To extact the fusesets use XeLL (shown below) or dump32.c.
XeLL Output
This shows the XeLL output from the serial cable method.
Xe>! XeLL - Xenon linux loader 0.1 * clearing BSS... * Attempting to catch all CPUs... CPUs online: 01.. CPUs online: 15.. * success. trying to initialize network... ok now the NIC NETIF at 8000000001459478 NIC reset reset: 01805508 1478 before: f2050000 1478: f2050000 init tx init rx starting httpd server..ok! * CPU PVR: 00710200 * FUSES - write them down and keep them safe: fuseset 00: c0ffffffffffffff fuseset 01: 0f0f0f0f0f0f0ff0 fuseset 02: 0f00000000000000 fuseset 03: c2666e8fab3c299a fuseset 04: c2666e8fab3c299a fuseset 05: c49a457d64ba4b3d fuseset 06: c49a457d64ba4b3d fuseset 07: f000000000000000 fuseset 08: 0000000000000000 fuseset 09: 0000000000000000 fuseset 10: 0000000000000000 fuseset 11: 0000000000000000
Downgrade
Downgrading is restricted by changing a lockdown counter in the NAND and the value of a fuset. If these two don't match, e.g lockdown counter is lower than the value of the fuseset, the machine refuses to boot.
It's possible to disable the change of the fuseset by removing power the the fuse and essentially disabling it.
It is still possible to downgrade if the fuseset has increased, but it requires CPU Key and altering of the old NAND dump to increase the lockdown counter. (As of 9th Aug. 2007 the CPU Key can only be found on a exploitable 4532 or 4548 system).
Counters
While upgrading to 4543 or 4552, fuseset #07 is changed and the lockdown counter in the NAND is increase by 1, for each update. I.e.:
Stock 2241: Lockdown counter: 0 Applied 4532: Lockdown counter: 1 Fuseset 07: f000000000000000 Applied 4552 Lockdown counter: 2 Fuseset 07: ff00000000000000
Fix lockdown counter
You can't directly flash a 4532 dump after updating to 4552. The fuseset has increased and the 4532 dump will not boot if the lockdown counter is lower than the fuseset, i.e refuses to boot if lockdown count > fuseset count.
To bypass this you need to decrypt the CF section of the 4532 dump and change the byte at 0x21F to something higher. The 360 Flash Dump Tool will patch and properly re-encrypt the flash image.